Vietnam’s growing reputation for cyber espionage has seen cybersecurity firms accuse the country’s state-sanctioned hackers of being responsible for attacks on everything from Toyota to the ASEAN Secretariat.
While China, Russia, Iran and North Korea have long been the world’s most active state-sanctioned cyber espionage players, Vietnam is increasingly being implicated for similar activities.
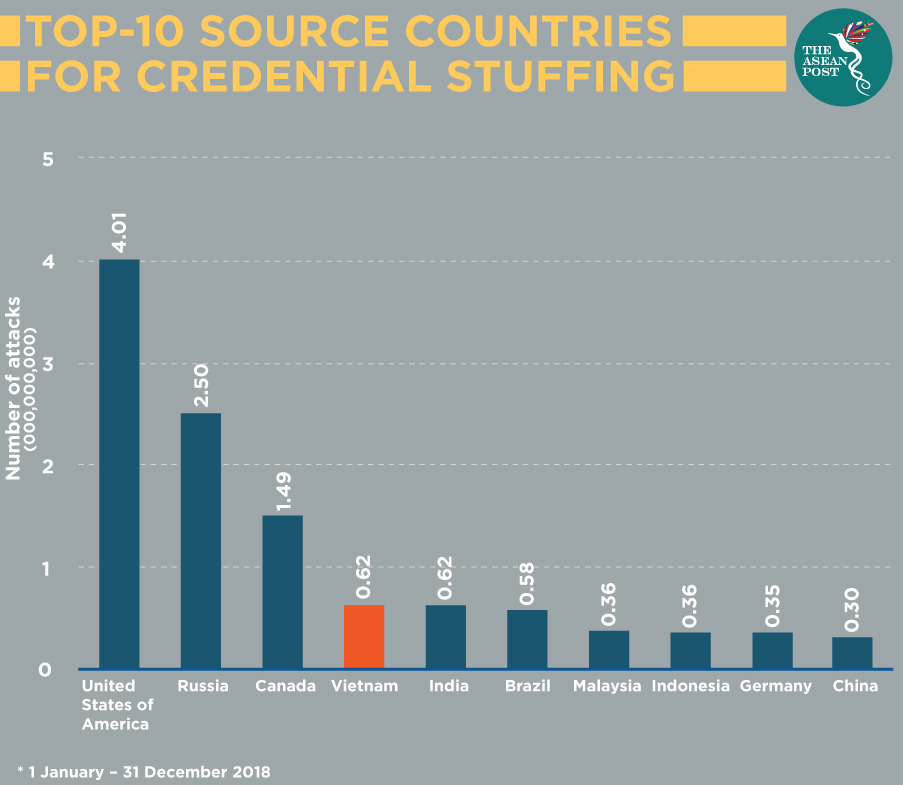
Vietnam was the fourth biggest source of credential stuffing last year – a sophisticated strike where hackers use specialised software to launch multiple automatic attempts to log into a website or app using stolen usernames and passwords – according to cloud services provider Akamai.
Responsible for some of the most notorious advanced cyber threats in Asia, the APT32 group is believed to be working on behalf of the Vietnamese government.
In 2017, cybersecurity company Volexity reported that APT32 had hacked ASEAN’s website during its annual summit, with the same group responsible for compromising websites of ministries or government agencies in Cambodia, Lao PDR and the Philippines.
In a June report titled ‘The rising Vietnamese Cybercriminal Landscape’, threat intelligence company IntSights agreed that APT32 targets foreign governments, businesses and dissidents for financial gain and to equip the regime with intelligence on its adversaries.
APT32 has been blamed for attacks against Vietnamese and Cambodian media outlets last year and was also credited with attacks on numerous automotive manufacturers ahead of VinFast’s – Vietnam’s first domestic auto company – planned debut.
Cybersecurity company FireEye has also noted that APT32 was actively targeting foreign multinationals and dissidents in Vietnam, and its activities were “of interest to the nation of Vietnam.”
In March, FireEye revealed that APT32 sent malicious lures to as many as 10 automotive manufacturing companies, noting that APT32’s hacking capabilities could help nurture its auto industry by gathering data on the competition.
The same month saw Toyota announce that five sales subsidiaries and three independent dealers in Tokyo had been hacked, exposing personal details of up to 3.1 million customers. Its subsidiaries in Vietnam and Australia also fell victim to similar breaches.
This is nothing new, and as far back as 2010, Google’s security blog reported that a malware which targeted Vietnamese computer users used the infected machines to spy on their owners as well as to participate in distributed denial of service (DDoS) attacks against blogs containing messages of political dissent.
Specifically, these attacks tried to squelch opposition to bauxite mining efforts in Vietnam, an important and emotionally charged issue in the country.
“While Vietnam may not have the resources to combat world superpowers – like China or the United States (US) – in traditional warfare or economic stature, cyber (warfare) is levelling the playing field,” said Charity Wright, an intelligence analyst at IntSights.
“Vietnam has the potential to develop into a cybercriminal outpost, as its government continues to censor the public and push its youthful middle class toward the fringes with its strict internet legislation,” she added.
Crushing dissent
An estimated 74 percent of Vietnamese access the internet daily according to Google. Fuelled by a rapidly expanding economy and a young population, the number of internet users in Vietnam has tripled to 49 million, or just over half of the population, in the last decade alone.
Since the dawn of the internet in Vietnam in 1997, the Communist Party of Vietnam (CPV) leadership has been concerned about the impact it would have on its ability to control information and combat dissent.
The Vietnamese government’s recent censorship legislation which came into effect at the start of the year requires social media companies to maintain local offices in Vietnam and store local user data within the country. If requested, they will also have to hand the data over to the government and remove content that the communist authorities deem to be “toxic”.
This is shepherding the younger generation into underground communities, and there has been an increase in Vietnamese-language internet traffic and activity on the deep and dark web with threat intelligence company IntSights observing underground forums fostering daily activity exceeding 10,000 unique users or more.
In order to block access to content that it deems unsavoury, the Vietnamese government has created a unit called Force 47 which comprises of some 10,000 members to enforce its cybersecurity law.
In his research paper published last week titled ‘The Political Economy of Social Media in Vietnam’, Dr Le Hong Hiep from the ISEAS-Yusof Ishak Institute noted how Force 47 is a major tool for the CPV and the government to maintain a “healthy” internet environment and to protect the regime against toxic information.
“In particular, members of this loosely organised force reportedly help to spread ‘positive’ information and counteract ‘negative’ views and fake news, especially those that are hostile to the ‘Vietnamese revolution’,” he said
“Force 47’s tasks range from collecting information on social media, to participating in online debates against ‘negative’ views, to reporting sites or social media accounts that spread fake news or unfavourable information,” he stated.
As IntSights’s Wright noted, this is an optimal time to be keeping a close eye on Vietnam, their economy, and their cyber operations - both state-sponsored and group.
Related articles:
Vietnam’s VinFast rolls out first car
